Twitter celebrates its 10th anniversary in 2016. In its relatively short life, the social media giant has garnered more than 1.3 billion registered users – nearly 18 percent of the world’s population. Of course, with so many Twitter-users, there are bound to be cyber security scams that pop up. One in particular is called impersonation.
Although reports state that the Twitter universe is inhabited by 1.3B members, the actual number of daily users is a modest 100 million, and 44 percent of people with a Twitter account have never actually tweeted anything. Still, Twitter has become an integral part of today’s online social world. About 46 percent of users log on at least once a day while 29 percent check Twitter more often than that. And despite the fact that many of the site’s users come from the millennial crowd, 83 percent of world leaders use Twitter – President Obama ranking first for usage.
By the numbers, it’s easy to see how Twitter impacts everyday life. There’s another statistic that’s worth noting, however, as it relates to one of the downsides to an always-on culture that depends on social media for connection. Between 5 and 10 percent of Twitter accounts are fake, depending on whom you ask. Researchers disagree with the total percentage, but even at 5 percent, that means that 10.75 million fake accounts exist in the Twitterverse. Why does it matter if Twitter allows fake accounts to exist? In a best-case scenario, fake accounts are annoying ploys created by spammers who want to increase sales using phony credentials. In a worst-case scenario, your identity could be stolen, duplicated and used without your knowledge to perpetrate serious cybercrime.
The Impact of Twitter Impersonation
Most cases of Twitter impersonation are harmless. Your friends may be playing a prank or some stranger three states away just wants to relieve his boredom. Those who impersonate celebrities or brands may want the attention that comes from falsely representing themselves as famous figures. For whatever reason, impersonation is a popular game on Twitter – but it’s not always a game.
In 2009, one of the most famous instances of Twitter impersonation involved St. Louis Cardinals general manager Tony La Russa. An imposter created a fake Twitter handle using La Russa’s name and photos and proceeded to tweet vulgar messages, including derogatory remarks against the Cardinals. La Russa sued Twitter over the impersonation, but the case was dropped without settlement after the social media site deleted the imposter account. The La Russa case highlighted the need for verified accounts for celebrities, a program that Twitter launched shortly after this debacle in 2009.
But what happens to ordinary people or those without substantial followers? Regular people living well outside the limelight can still be impersonated, and the impact can be devastating even if no money changes hands. Twitter impersonation can ruin your online reputation – with friends, family and even potential employers. In one notable example, journalist Cale Guthrie Weissman discovered a Twitter impersonator who was bent on “besmirching [his] journalistic honor” by tweeting about Weissman’s incompetence and alleged misconduct. Weissman reported the imposter, but Twitter’s insufficient response prompted the journalist to question the social media site’s commitment to protecting its users.
JoBeth McDaniel of The Daily Beast faced a similar issue when her Twitter account was parodied by a bored imposter who spent weeks tweeting inappropriate content and drivel under the guise of a respected writer. The imposter account garnered more followers than the real entity herself, and McDaniel feared that her online reputation – and her job prospects – would be trampled by someone who was simply passing the time.
Blogger Nick from DataGenetics posted about his experience reporting an imposter account on Twitter, which turned out to be a lesson in extreme patience as the company took eight days to resolve the issue. In an age of lightning-fast communication, eight days is enough time to cause serious damage if a cybercriminal is motivated enough. These and countless other examples emphasize the need for greater security measures from social media sites, but they also highlight the need for users to pay attention to how they appear online. Whether it’s a simple joke or a ploy for extortion, Twitter impersonation is no laughing matter.
Twitter’s Policy on Fake Accounts
As a company, Twitter takes a liberal view of its posting guidelines: “We believe that everyone should have the power to create and share ideas and information instantly, without barriers.” Despite the open policy on content and use, Twitter takes a hard stance against certain types of behavior. Listed under “abusive behavior,” impersonation is considered any conduct that “is intended to or does mislead, confuse, or deceive others.” If you come across a fake account with your name and picture – but not your tweets – then this is considered impersonation. Likewise, brand and celebrity impersonations that attempt to defraud viewers are also considered abusive behavior. There are a couple of exceptions to Twitter’s rules on impersonation:
• A shared name does not count as misconduct as long as one person isn’t trying to defraud the other person or other Twitter users.
• Parody accounts are allowed as long as the account-holder makes it clear that the account is in jest or is unrelated to the person, business or entity that’s being parodied.
Similar profile pictures, avatars, themes and content aren’t necessarily against the rules. With millions of active daily users on Twitter, you’re bound to come across someone who thinks, tweets and even looks like you or someone you know. But intentions matter when it comes to duplicate accounts. If your doppelganger is purposely trying to deceive other users, then you have a case for impersonation. Once Twitter determines that an account is deliberately violating the impersonation rules, that account could be permanently suspended at Twitter’s discretion.
Reporting Abuse
If you discover that someone’s intentionally impersonating you on Twitter, you can report it using the steps outlined on Twitter’s support page. Unlike with some sites, such as Snapchat or Facebook, you don’t even have to have a Twitter account to report impersonation. You can also report misconduct on behalf of another user, which is different from most social media sites. Instagram, for example, does not allow third-party reporting unless the issue is related to minors. The reporting process is as follows:
• Submit an impersonation report either from the account page directly or through the impersonation support page on Twitter.
• Verify your personal information. You’ll need to submit a copy of a government-issued ID, like your driver’s license. This is usually done via fax.
• Once you submit the report, Twitter will conduct an investigation into the alleged misconduct. If Twitter determines that the account is fraudulent, the fake account will be taken down and most likely suspended indefinitely. Alternately, someone who’s violating the rules unintentionally may just be asked to update the account so that it adheres to the rules.
It’s a good idea to take a screenshot of the imposter account for your own records and to help Twitter identify the misconduct if there’s a problem. Make sure the screenshot has a time and date stamp.
On a related note, if you try to sign up for a Twitter account only to discover that your username, email address or phone number is already in use, it doesn’t necessarily mean that there’s foul play afoot. Double check that you didn’t sign up in the past – it happens – and proceed from there. Twitter’s support team can help you sort out what’s going on.
How to Prevent Twitter Impersonation
Twitter makes it easy to identify fake celebrities, brands and other media icons. According to the support page, Twitter verifies accounts of “key individuals and brands.” These include “highly sought users in music, acting, fashion, government, politics, religion, journalism, media, sports, business and other key interest areas.”
If a Twitter account has a blue check mark icon next to the name, then it’s a verified account. If you see a major brand, such as Coca-Cola or Nike, tweeting without this blue check mark, then chances are the account isn’t real. Smaller brands and lesser-known celebrities may not have been verified yet, so proceed with caution if a name you love doesn’t have that blue check mark.
The best way to deal with Twitter impersonation is to prevent it from happening in the first place. Even if you don’t use Twitter, there are ways to keep your information from falling into the wrong hands. Here are some good tips for reducing the chances of identity theft:
• Create strong, random passwords that aren’t associated with aspects of your life, like your pet’s name or mother’s maiden name. Use different passwords for varying email and social media accounts. Likewise, keep security question answers private and non-personal. Make up the answers so that they can’t be easily guessed by someone who knows you.
• Every so often, search for yourself online using a service like Pipl or a more generic search engine like Bing or Google. You can only do something about impersonations if you know what’s out there to begin with.
• Keep your email address private. Don’t list it on your contact information. If you need to list it for work or other reasons, use a separate email that isn’t tied with any personal data. Twitter impersonators only need an email to register, so keep yours safe and secure.
If you do stumble across suspicious Twitter activity, know the ways to spot a fake account. Generic profile pictures, a lack of bio, excessive tweets with the same content, few followers and an unrealistic number of tweets are among the ways that you can tell when a profile is phony. Look out for your friends, too. If you notice that your Twitter pals are posting odd tweets or following people they may not normally follow, then let them know. The key to stopping impersonation is vigilance.

 Fake Profile Pictures
Fake Profile Pictures  YouTube Impersonation
YouTube Impersonation  Pinterest Impersonation
Pinterest Impersonation  Snapchat Impersonation
Snapchat Impersonation  Copyright Protection
Copyright Protection  Spambots
Spambots 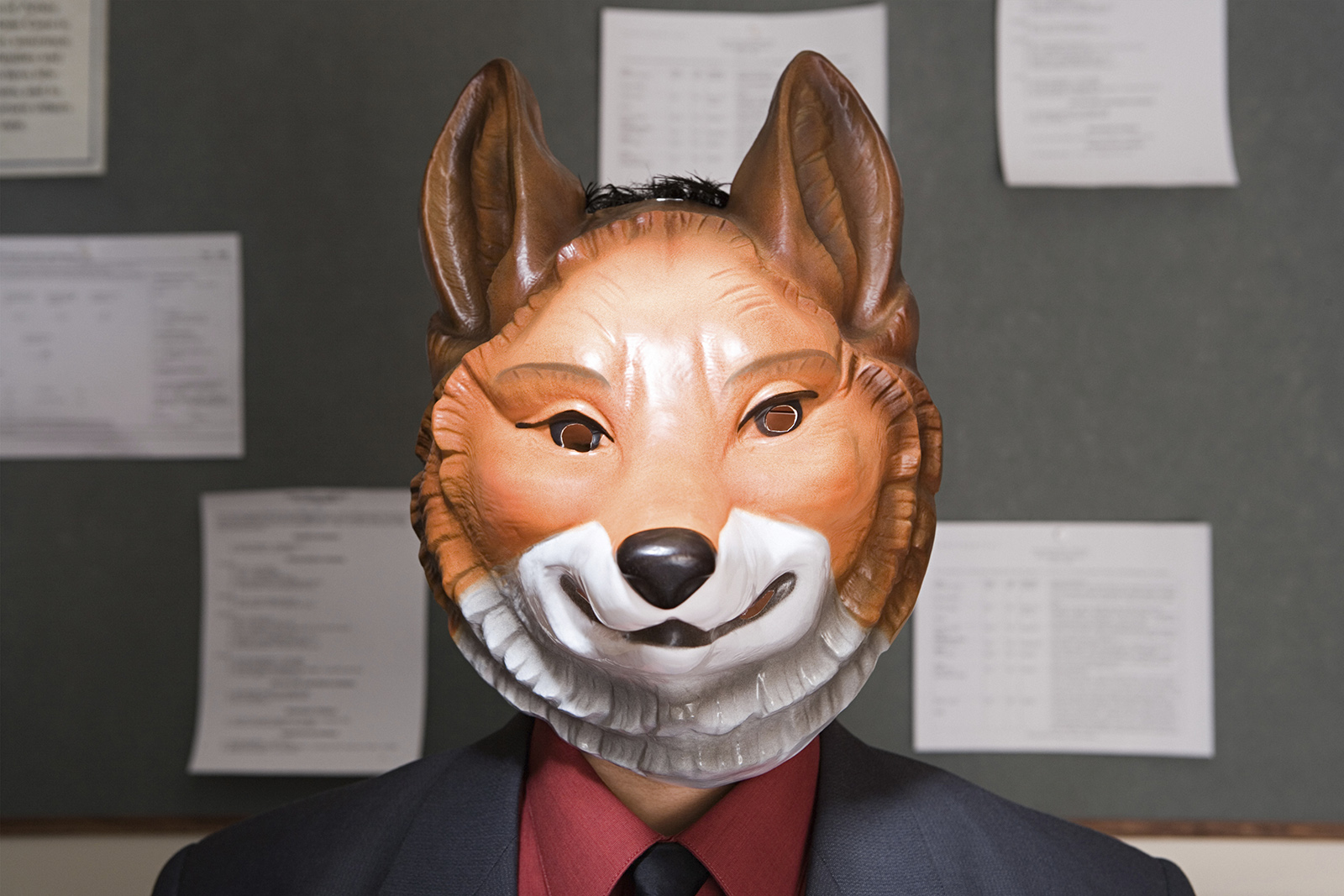 Catfishing
Catfishing  Facebook Hacking
Facebook Hacking