On September 9, 2014 a user named tvskit posted a “credential dump” of 4.92 million Gmail accounts and passwords on a Russian Bitcoin Security Forum.
Unfortunately, credential dumps are common place in today’s Internet environment. This particular dump was posted to the Russian Bitcoin Security Forum by user tvskit with the assistance of an administrator named “polym0rph”. The publisher posted a screenshot of the database and claimed that sixty percent of the passwords were active and functioning. Over the next few days the Russian Bitcoin Security Forum had several more postings of credential dumps in the form of a text file which contained an estimated 1.26 million log-in credentials for Yandex users, Russia’s largest search engine and 4.65 million of Mail.ru accounts. Since the dump was discovered a forum administrator has removed the passwords from it, for what many see as too little, too late.
According to the Russian media outlet CNews an investigation of the credential dumps showed the majority of the account data that were obtained belong to English, Russian, and Spanish speaking users of the Google email provider service. The investigation revealed that only about two percent of the credential dump may have been active and would possibly work, that would be approximately 10,000 of the five million that were posted on the Bitcoin Security Forum.
It was also determined that the credentials dumped on the Russian Bitcoin Security Forum were gathered from a combination of older, various credential dumps collected over a time span that indicated the hack was from an unrelated website, not Google.
Google published the following acknowledgement on a blog post:
One of the unfortunate realities of the Internet today is a phenomenon known in security circles as “credential dumps”—the posting of lists of usernames and passwords on the web. We’re always monitoring for these dumps so we can respond quickly to protect our users. This week, we identified several lists claiming to contain Google and other Internet providers’ credentials.
We found that less than 2% of the username and password combinations might have worked, and our automated anti-hijacking systems would have blocked many of those login attempts. We’ve protected the affected accounts and have required those users to reset their passwords.
It’s important to note that in this case and in others, the leaked usernames and passwords were not the result of a breach of Google systems. Often, these credentials are obtained through a combination of other sources.
For instance, if you reuse the same username and password across websites, and one of those websites gets hacked, your credentials could be used to log into the others. Or attackers can use malware or phishing schemes to capture login credentials.
Cyber criminals often use these types of credential dumps claiming to have an altruistic purpose, to shame the company into utilizing better cyber security measures or to warn the company’s customers about cyber vulnerabilities, when in fact it is for the purpose of phishing scams.
Gmail users should be very wary of any emails or websites claiming to check to see if your email credentials have been compromised. Typically they are sites set up by the very criminals that posted the credentials dump, in order to steal more identity data. One such site that has popped up is a Russian website isleaked.com whose domain name was registered on September 8, 2014 and is suspected of being operated by the hackers. The best course of action is to change your email username and password and make certain not to reuse them for other sites. Do not click on any links sent by email from any provider service, no matter how authentic they appear, go directly to the official website.
Additional Resources About This Breach:
http://www.pcworld.com/article/2605400/five-million-gmail-addresses-and-passwords-dumped-online.html
http://www.dailydot.com/crime/google-gmail-5-million-passwords-leaked/
https://bitcointalk.org/index.php?topic=777549.0;all
http://cointelegraph.com/news/nearly-5m-gmail-credentials-leaked-on-russian-bitcoin-security-forum

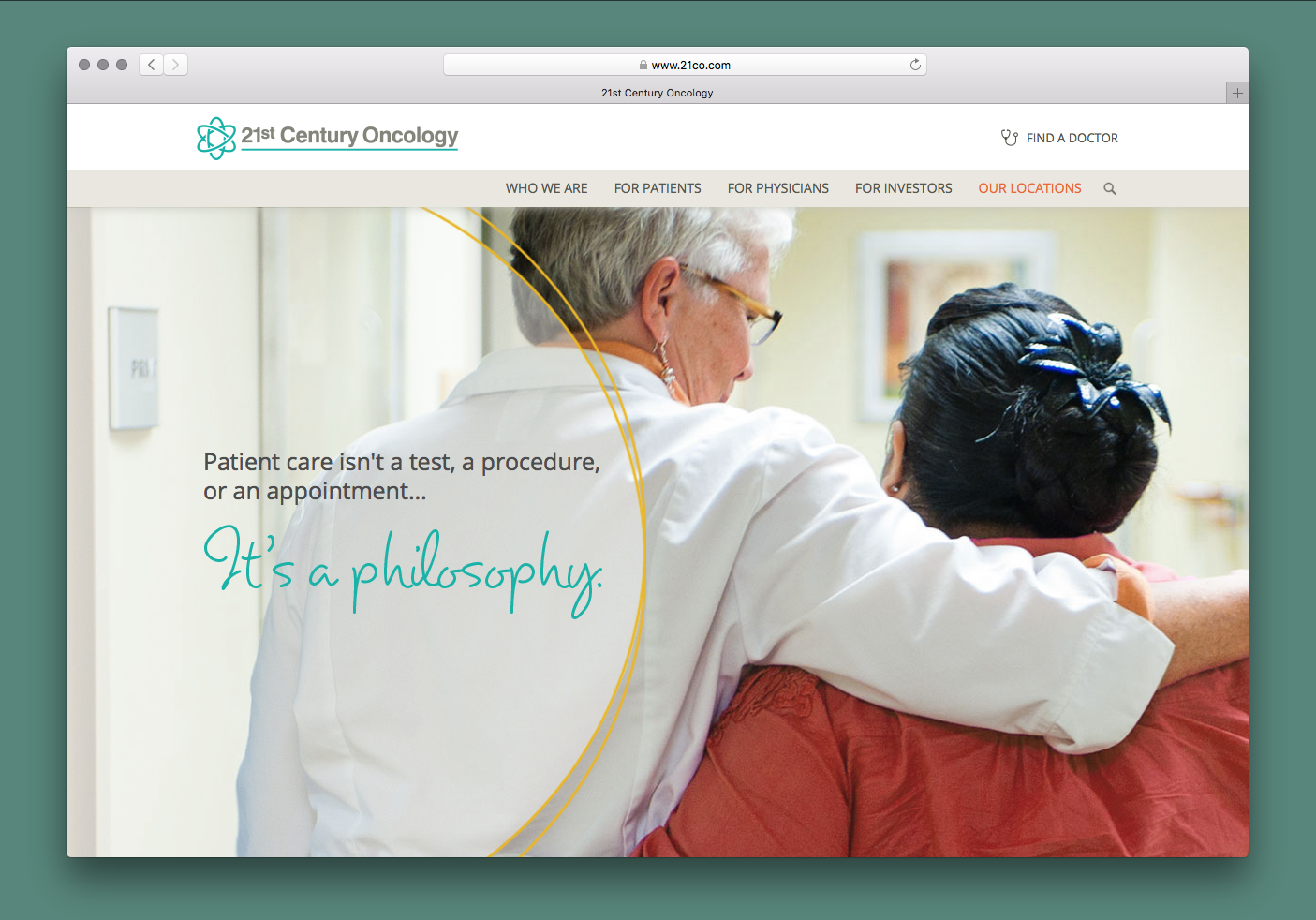 21st Century Oncology Group Breach
21st Century Oncology Group Breach  Advocate Medical Group Breach
Advocate Medical Group Breach 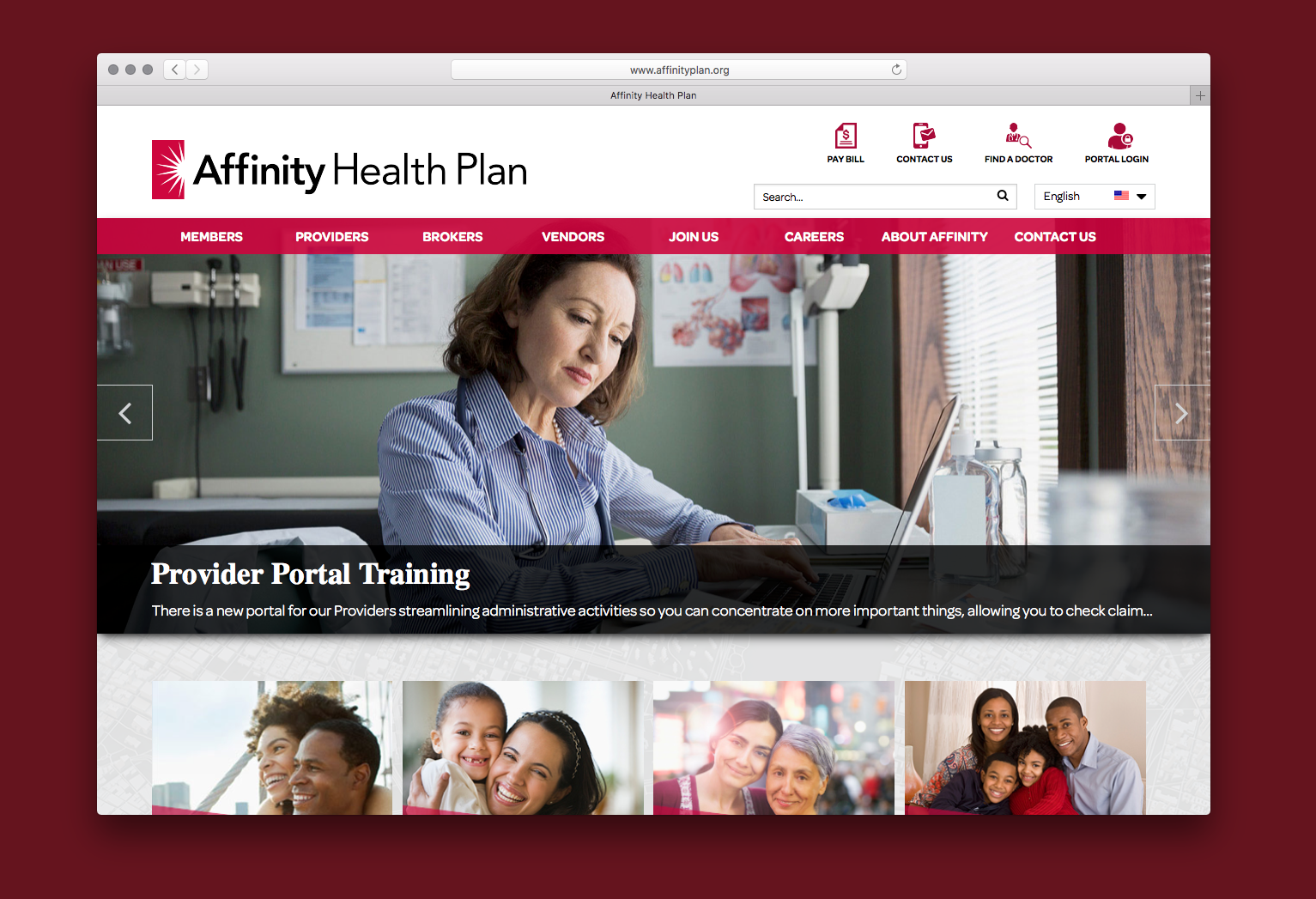 Affinity Health Plan
Affinity Health Plan  126 Email Service
126 Email Service  000webhost.com
000webhost.com  17 Streaming App
17 Streaming App  7K7K
7K7K  Equifax Data Breach
Equifax Data Breach 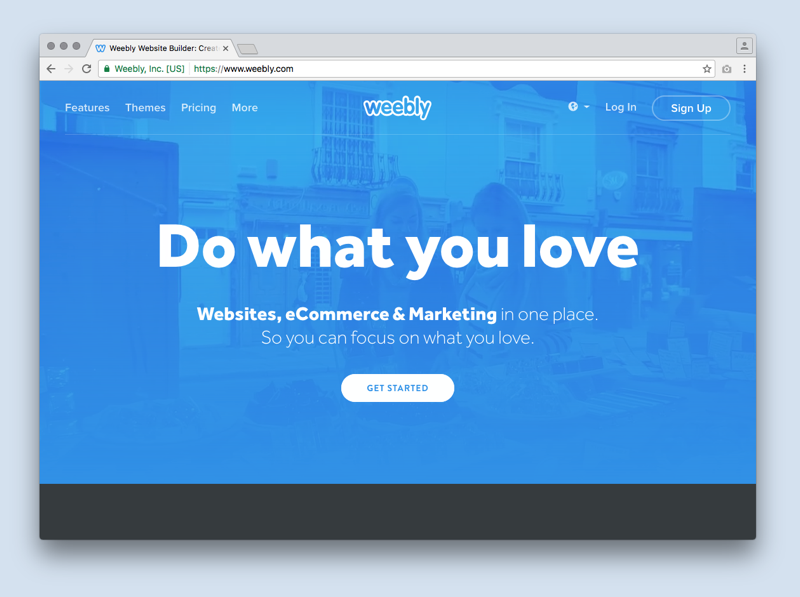 Weebly
Weebly  Yahoo!
Yahoo!  NY Times Russian Cyber Breach
NY Times Russian Cyber Breach  Vivint
Vivint