Paddy Power, an Irish bookmaker, which conducts business both offline with a chain of licensed bookmaking (betting) shops in the United Kingdom and Ireland, as well as online and telephone betting services in Ireland has today announced a data breach that dates back to 2010.
In its statement Paddy Power uses the terminology “historical data breach” because the breach they reference is from 2010. The company has stated they are actively pursuing contact of at least 649,055 of its customers they believe may have possibly been affected, to notify them of the incident.
The data breach included the names, user names, phone numbers, addresses, email addresses, dates of birth, and related prompted security questions. Paddy Power has stated that no credit, debit card, or other financial information has been exposed during the breach.
Additionally, it should be noted that according to Paddy Power the information that was exposed during the breach, or potentially breached back in 2010 would not allow the cyber criminals to access a Paddy Power customer’s account. According to Paddy Power the cyber security breach would not affect customers who had joined after 2010, and that their customers who used their services after this date have never been at risk for exposure to their account information.
Power Paddy has not revealed why the company did not inform its customers in 2010 of the cyber breach to its network systems even though they were aware of the malicious activities of the cyber thieves. Paddy Power’s response was to conduct a security audit and update its security protocols without giving notice to its users. The company has said they didn’t understand the depth of the cyber intrusion when it occurred in 2010, but still provided no answer as to why customers were not informed of the breach before now, nearly four years later.
What is now known about the Paddy Power breach is that an individual third party became aware of the 2010 data breach by way of a person in Canada who possessed sensitive data of Paddy Power’s customers. After Paddy Power verified that the data was genuine and in fact originated from their own network systems, the company contacted law enforcement authorities to bring about a possible criminal investigation.
Once the Data Protection Commissioner had been made aware of the incident, Paddy Power then (in July of 2014) began notifying it’s customers of the cyber breach that occurred in 2010.
The lack of transparency to it’s customers on the part of Paddy Power is very concerning, but still within the law. The Data Protection Commissioner has a set of standards called “a code of practice” to guide companies in their response to data breaches, but the code companies are to adhere to is voluntary and not required by law. The commissioner’s agency does not have the legal authority to impose fines or charge entities (companies) that do not adhere to the code of practice, which leaves cyber security experts in the field wondering why there is an agency at all if not to see that companies who are breached are forthcoming with its potential victims?
For your convenience and perusal we have included the following statement made by Paddy Power to its customers below:
PADDY POWER ADVISES CUSTOMERS OF HISTORICAL DATA BREACH
31 Jul 2014
– No financial information or customer passwords accessed in hacking incident
– Full investigation shows no evidence customers’ accounts adversely impacted
– Incident restricted to a number of customers who held an account in 2010, no impact on customers who opened accounts after this timePaddy Power is today (Thursday, 31st July 2014) contacting certain customers in relation to an historical data breach. No financial information or customer passwords were compromised in the isolated incident and customers’ accounts are not at risk as a result. The full extent of the 2010 data breach became known to the Company in recent months when it took legal action in Canada with the assistance of the Ontario Provincial Police to retrieve the compromised dataset from an individual.
Paddy Power takes its responsibilities regarding customer data extremely seriously and it is deeply regrettable that this breach happened. Paddy Power has engaged with the Office of the Data Protection Commissioner on this issue and kept them updated on the action taken by the Company.
The historical dataset contained individual customer’s name, username, address, email address, phone contact number, date of birth and prompted question and answer. Customers’ financial information such as credit or debit card details has not been compromised and is not at risk. Account passwords have also not been compromised. Paddy Power’s account monitoring has not detected any suspicious activity to indicate that customers’ accounts have been adversely impacted in any way.
The accessed information alone would not have been sufficient to grant access to a Paddy Power customer account and this incident has no impact on customers who opened accounts after 2010.
Paddy Power is today pro-actively contacting 649,055 affected customers on this issue. Customers are being advised to review other sites where they use the same prompted question and answer as a security measure and update where appropriate.
We sincerely regret that this breach occurred and we apologise to people who have been inconvenienced as a result. We take our responsibilities regarding customer data extremely seriously and have conducted an extensive investigation into the breach and the recovered data. That investigation shows that there is no evidence that any customer accounts have been adversely impacted by this breach. We are communicating with all of the people whose details have been compromised to tell them what has happened.
Robust security systems and processes are critical to our business and we continuously invest in our information security systems to meet evolving threats. This means we are very confident in our current security systems and we continue to invest in them to ensure we have best in class capabilities across vulnerability management, software security and infrastructure.
Additional Resources About This Breach:
http://www.paddypowerplc.com/media/news/paddy-power-advises-customers-historical-data-breach
http://www.independent.ie/business/irish/massive-data-breach-at-paddy-power-bookmakers-30474614.html
https://www.clearswift.com/blog/2014/08/07/paddy-power-data-breach-good-bad-recommendations

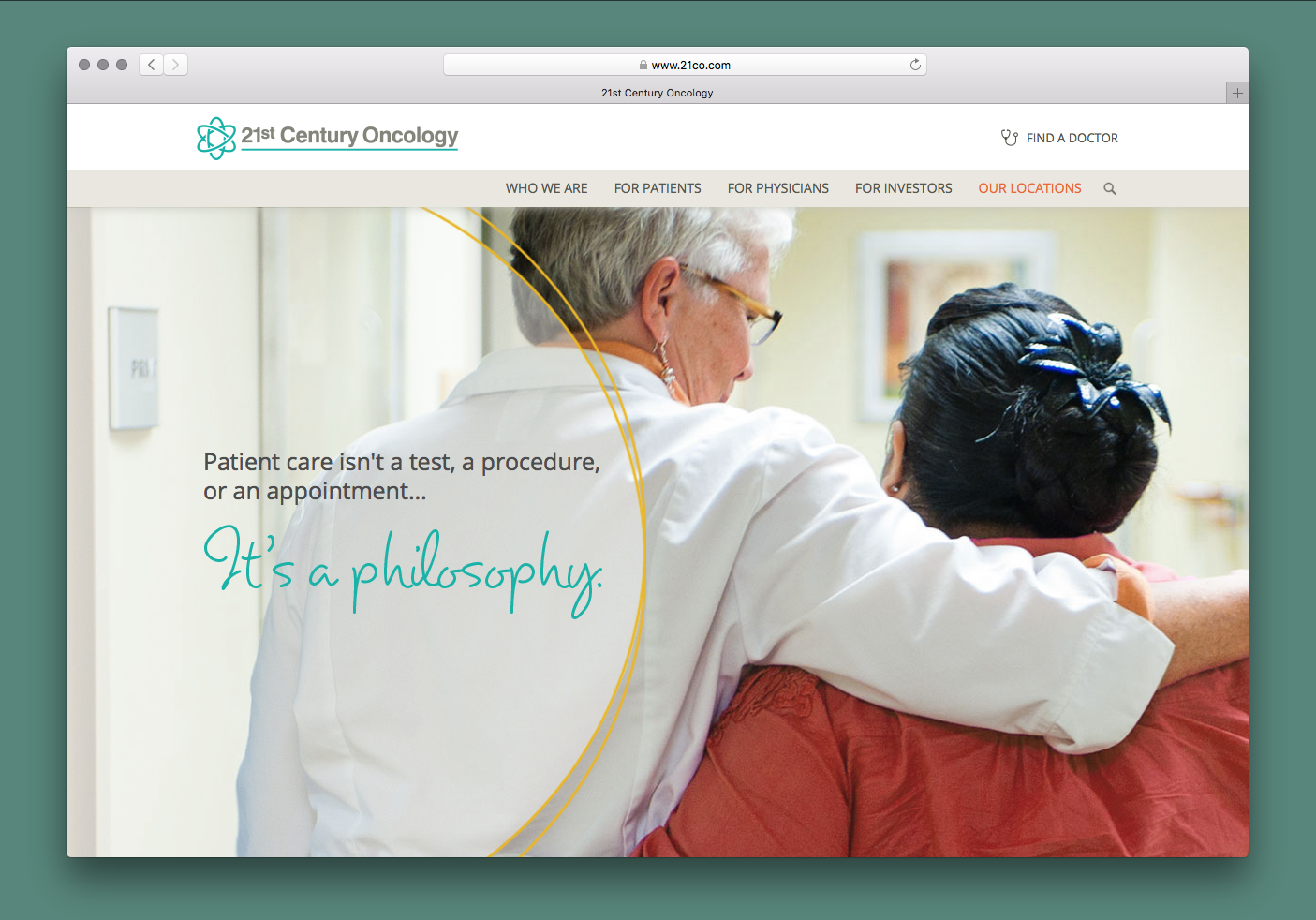 21st Century Oncology Group Breach
21st Century Oncology Group Breach  Advocate Medical Group Breach
Advocate Medical Group Breach 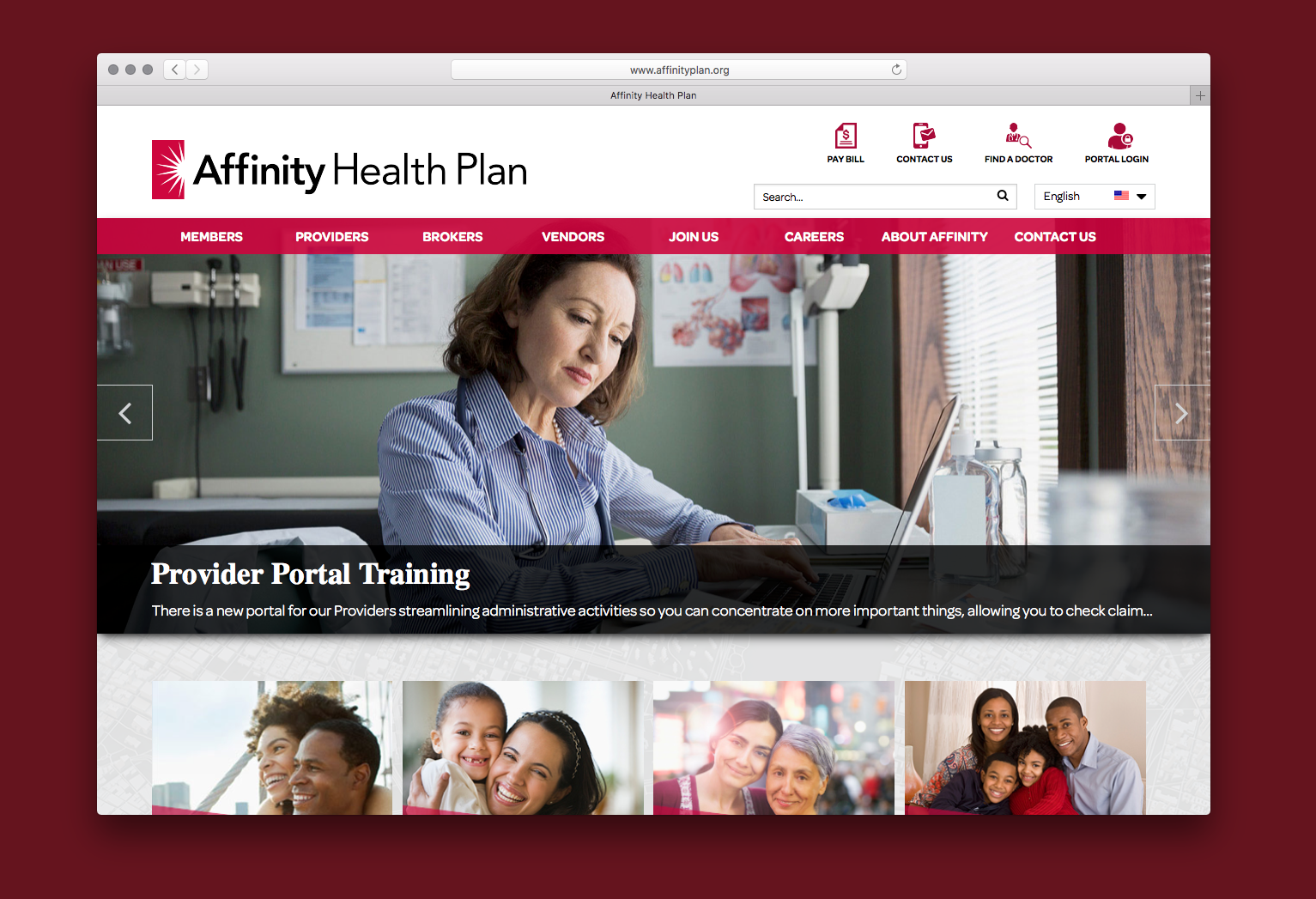 Affinity Health Plan
Affinity Health Plan  126 Email Service
126 Email Service  000webhost.com
000webhost.com  17 Streaming App
17 Streaming App  7K7K
7K7K  Equifax Data Breach
Equifax Data Breach 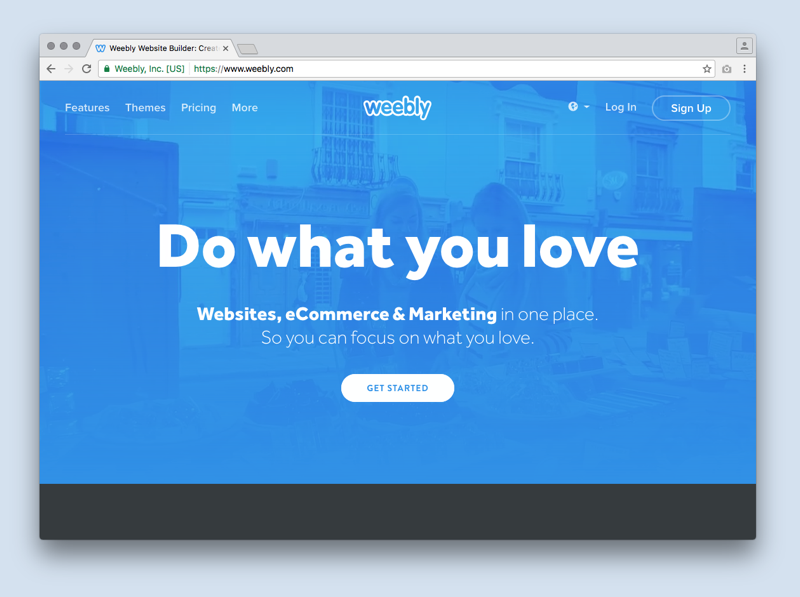 Weebly
Weebly  Yahoo!
Yahoo!  NY Times Russian Cyber Breach
NY Times Russian Cyber Breach  Vivint
Vivint