In February 22nd, 2014, Deletesec announced that data belonging to Connecticut-based Spirol Fastening Solutions had been compromised. The hackers went by a user name of @Deletesec according to their Twitter account. The compromised data included email addresses, job titles, employers’ details, and phone numbers among many others. Spirol Company is known to serve a lot of high profile personnel and companies across the globe. As a result, more than 30,000 companies being served by Spirol were announced to be affected. Credentials belonging to these enterprises were leaked online. Spirol is an international company that specializes in the fasting industry. The manufacturer specializes in the manufacture and distribution of brass nuts, pins, and inserts for plastic components. The hacking was announced on Twitter by @Deletesecs who posted the news on his Twitter account.
Three CSV files were also displayed to the media fire. The three files had a total size of 27mbs, and it contained a heap of data which most came from a file called CRM_data. CRM_data provides plenty of client’s confidential account information together with their contact details. The hackers said the reason behind them carrying out the attack was due to Spirol’s threats to have them arrested. The claim shows that Spirol were aware of the breach before it was leaked online but they could not stop it. The total number of email addresses leaked was 70,889 of which 886 had passwords while the rest were set as blank. The leaked data also had 31,123 company names with their details. More than 25,000 different email providers also fell victim of the incident.
The other two files contained more 96 accounts with usernames, email addresses, and clear text passwords.
The stolen data was analyzed by Cyber War News, which found out that the data contained the names of 31,123 companies along with 27,000 email addresses. Prominent names were in the list of them large enterprises such as Ford, Tesla, GM, and Harley Davidson. Other information that was leaked included 96 usernames, email addresses, and transparent test passwords, which is thought to belong to the company’s employees. The attackers claimed to have gained access through an SQL injection. SQL injection is the most popular, method that is always associated with database leaks. The attack was carried out by exploiting the SQL injection vulnerability that led to yielding of the data from Spirol’s CRM system. The data obtained ranged from customer’s names, contact information, together with more than 55,000 exclusive email addresses.
Reference.
www.cyberwarnews.info/2014/02/22/spirol-hacked-70889-clients-information-leaked-after-being-warned?/utm_source=AnonFriends&utm_medium=AF

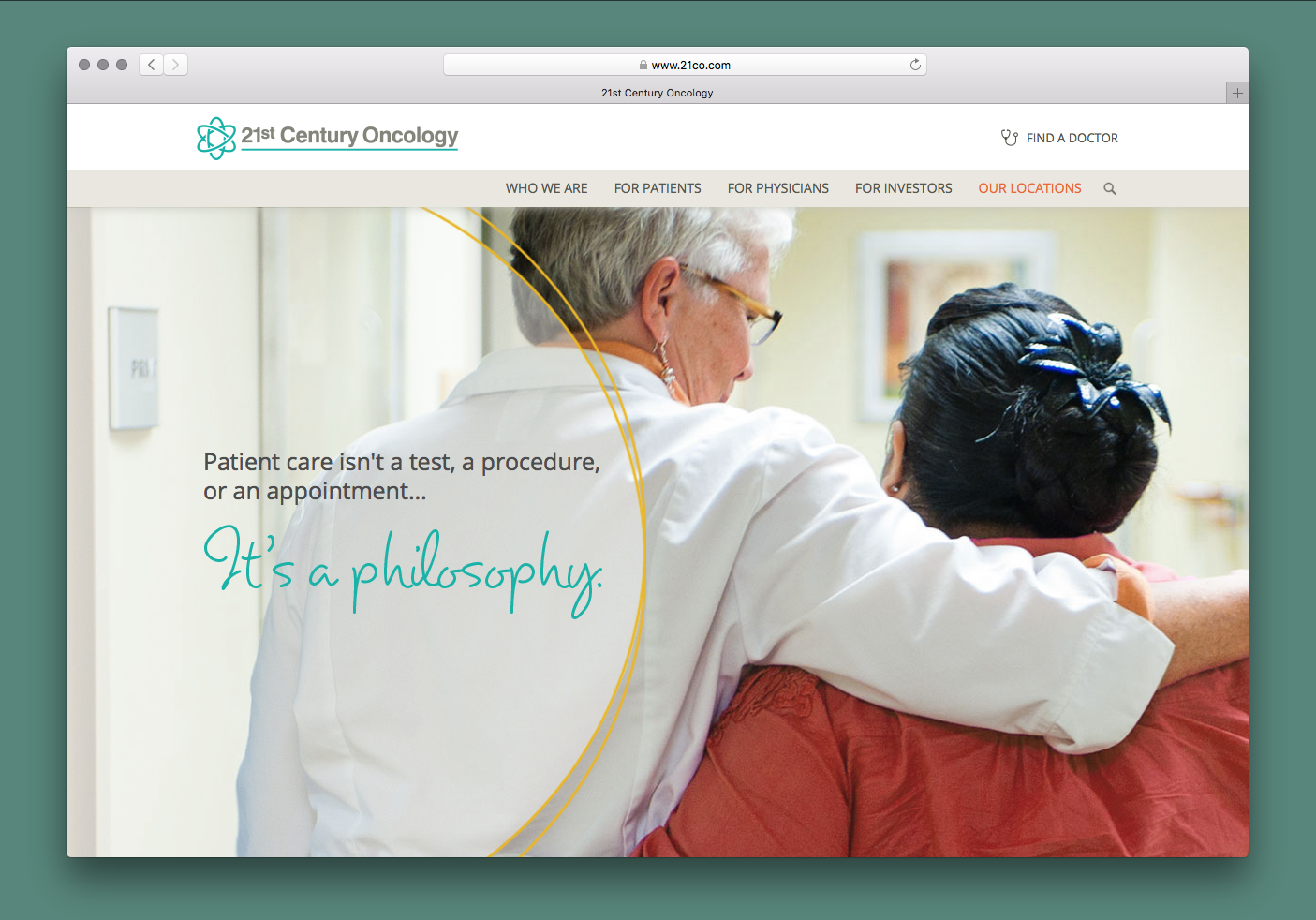 21st Century Oncology Group Breach
21st Century Oncology Group Breach  Advocate Medical Group Breach
Advocate Medical Group Breach 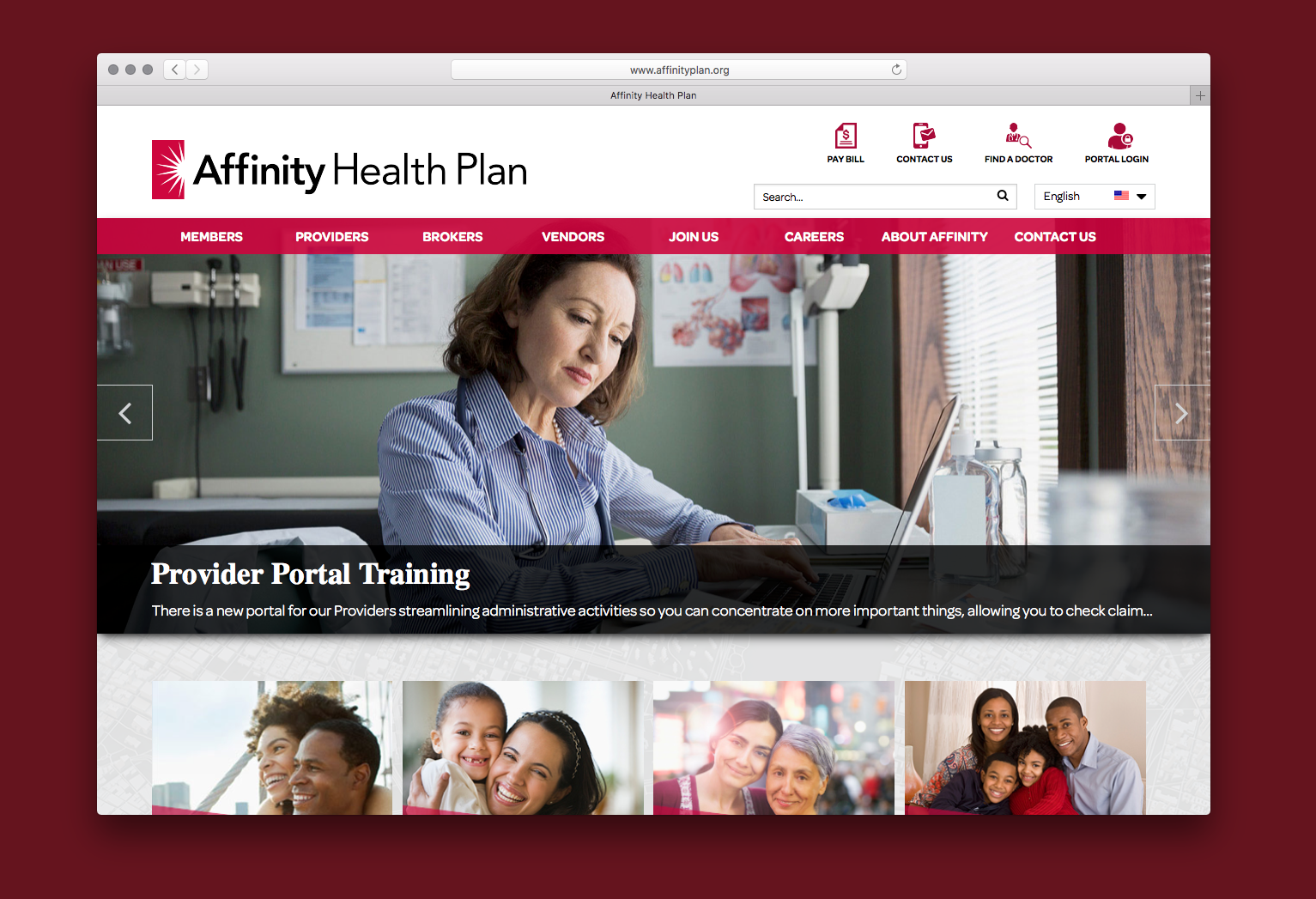 Affinity Health Plan
Affinity Health Plan  126 Email Service
126 Email Service  000webhost.com
000webhost.com  17 Streaming App
17 Streaming App  7K7K
7K7K  Equifax Data Breach
Equifax Data Breach 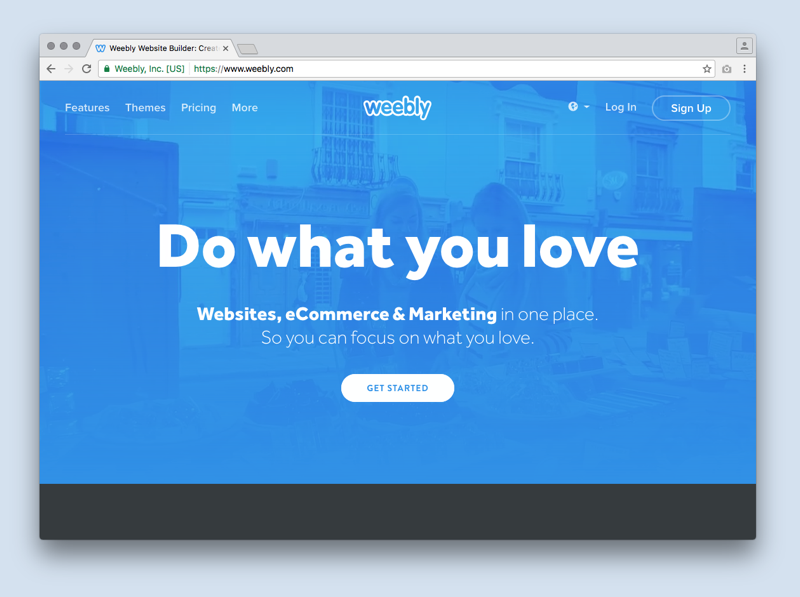 Weebly
Weebly  Yahoo!
Yahoo!  NY Times Russian Cyber Breach
NY Times Russian Cyber Breach  Vivint
Vivint